“… this thing calling itself “PuTTY” was written by a developer who might know how to implement RSA in C, but who does not know how or why to use RSA.”
Category Archives: Security tips
United Airlines offers air miles for vulnerability information
United Airlines has become the first airline to start a bug bounty program, offering air miles for for remote code execution bugs, authentication bypasses, timing attacks, etc.
Only members of its MileagePlus program can apply, so bug hunters who aren’t will have to become members before sending in their submission.
The bug bounty program encourages researchers to find vulnerabilities in the company’s customer-facing websites, its app, and third-party programs loaded by united.com or its other online properties.
Bugs that only affect legacy or unsupported browsers, plugins or operating systems will not be taken into consideration for rewards, and so will not bugs on the company’s internal sites, partner sites, or bugs on onboard Wi-Fi, entertainment systems or avionics.
Source: United Airlines offers air miles for vulnerability information
Solid-state drives lose data if left without power for just a few days | ZDNet
Solid-state drives are great for performance, but data security must come first.
New research suggests that newer solid-state hard drives, which are faster and offer better performance, are vulnerable to an inherent flaw — they lose data when they’re left dormant in storage for periods of time where the temperature isn’t properly regulated.
The worrying factor is that the period of time can be weeks, months, but even in some circumstances — just a few days.Solid-state drives are better than regular mechanical hard drives, which are slow and sluggish. But unless they’re battered around, smashed, or poured in acid, they pretty much last forever.
A recent presentation by hard drive maker Seagate’s Alvin Cox warned that the period of time data is retained on some solid-state drives is halved for every 9°F (or 5°C) rise in temperature where its stored.
That means if a solid-state drive is stored in a warm room, say 77°F (25°C), its data can last for about two years. But, if that goes up by a mere few degrees to 86°F (30°C), that data’s retention period will be cut in half.
Source: Solid-state drives lose data if left without power for just a few days | ZDNet
Easily Cracking a Master Combination Lock
Kamkar told Ars his Master Lock exploit started with a well-known vulnerability that allows Master Lock combinations to be cracked in 100 or fewer tries. He then physically broke open a combination lock and noticed the resistance he observed was caused by two lock parts that touched in a way that revealed important clues about the combination. (He likened the Master Lock design to a side channel in cryptographic devices that can be exploited to obtain the secret key.) Kamkar then made a third observation that was instrumental to his Master Lock exploit: the first and third digit of the combination, when divided by four, always return the same remainder. By combining the insights from all three weaknesses he devised the attack laid out in the video.
Source: Schneier on Security: Easily Cracking a Master Combination Lock
Year-old flaw in popular WordPress plugin still actively exploited
Sucuri Security researchers have discovered yet another malicious campaign redirecting users to sites hosting exploits. As per usual, the attackers are mostly leveraging vulnerabilities in WordPress plugins to compromise sites that will become the first link of the redirection chain.
In this particular campaign, the attackers took advantage of the fact that the site admins still use an old version Slider Revolution (RevSlider) plugin, which contains a critical vulnerability that allows attackers to compromise websites via their database.
“Please don’t think that only the Slider Revolution plugin need to be updated,” the researchers entreated. “Keep all of your plugins and themes up-to-date. Any plugin can have critical vulnerabilities at any given time, known or unknown. Even the most popular plugins can have security issues.”
Source: Year-old flaw in popular WordPress plugin still actively exploited
Las Vegas’ Hard Rock casino hit by carders
Las Vegas’ popular Hard Rock Hotel and Casino has been hit by carders, who took off with names, card numbers, expiration dates, and CVV codes (but not PIN numbers or other information) of customers who used their payment cards at several locations within the property.
Not much detail has been offered about how the breach happened, but it’s likely that POS malware has been installed at the affected locations.
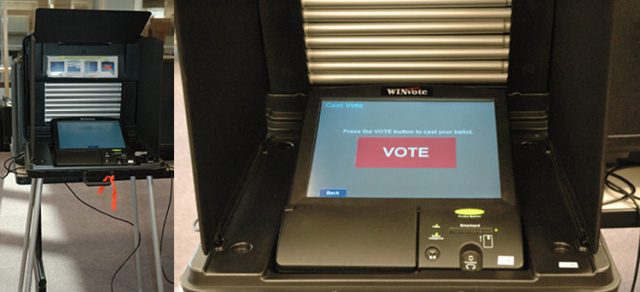
Easy to hack e-voting machine
The weak passwords — which are hard-coded and can’t be changed — were only one item on a long list of critical defects uncovered by the review. The Wi-Fi network the machines use is encrypted with wired equivalent privacy, an algorithm so weak that it takes as little as 10 minutes for attackers to break a network’s encryption key. The shortcomings of WEP have been so well-known that it was banished in 2004 by the IEEE, the world’s largest association of technical professionals. What’s more, the WINVote runs a version of Windows XP Embedded that hasn’t received a security patch since 2004, making it vulnerable to scores of known exploits that completely hijack the underlying machine. Making matters worse, the machine uses no firewall and exposes several important Internet ports.
Source: Meet the e-voting machine so easy to hack, it will take your breath away | Ars Technica
How secure are digital transactions?
The online payment industry was exposed to a slew of attacks in 2013-14, with hackers meticulously examining the payment infrastructure to exploit potential weaknesses. To guard against such security breaches, the payment industry needs to devise global security initiatives and establish common rules.
Until the recent spate of attacks, banks and financial institutions had been reluctant to invest heavily in protecting their digital transactions. However, new awareness of the huge liabilities and losses that can be incurred through these data leaks is encouraging their support for the use of HCE security technology.
Unpatched, vulnerable PDF readers leave users open to attack
Unpatched, vulnerable PDF readers are a big security issue for private PC users, according to Secunia. 14% of PC users in the US (up from 12.9% last quarter) have an unpatched operating system, and that Oracle Java yet again tops the list of applications exposing PCs to security risks.
The security of a PC is significantly affected by the number and type of applications installed on it, and the extent to which these programs are patched:
- Adobe Reader 10 and 11 come in at number three and four on the Most Exposed List. Adobe Reader 10 with a 25% market share, 39 vulnerabilities and unpatched on 65% of PCs. Adobe Reader 11 with a 55% market share, 40 vulnerabilities and unpatched on 18% of PCs.
- Oracle’s Java JRE 7 tops the list as the most exposed application on the US PCs. With a market share of 54%, 77% of users have not installed the latest updates, despite 101 reported vulnerabilities.
- 1 in 20 programs on the average US PC have reached end-of-life, meaning they are no longer supported by the vendor and do not receive security updates. Adobe Flash Player, one of the end-of-life applications, is still installed on no less than 78% of the PCs.
- Other applications in the top 10 include Apple QuickTime, Microsoft Internet Explorer and uTorrent for Windows.
Source: Unpatched, vulnerable PDF readers leave users open to attack
Hacker Implants NFC Chip In His Hand To Bypass Security Scans And Exploit Android Phones – Forbes
Hackers who want real stealth might want to hack their own body first. An ex-military security specialist tells FORBES an NFC chip in his hand would be a useful tool in any digital criminal’s arsenal, showing off an exploit attacking an Android phone. Is evil biohacking about to go mainstream?
Source: Hacker Implants NFC Chip In His Hand To Bypass Security Scans And Exploit Android Phones – Forbes